The VoIP landscape is constantly evolving, and with that comes new vulnerabilities. In this blog post, we’ll discuss some of the most common VoIP vulnerabilities and how you can protect your system against them.
Checkout this video:
Introduction
Voice over Internet Protocol (VoIP) is a popular technology that allows users to make telephone calls using a broadband Internet connection instead of a traditional analog phone line. VoIP has many advantages over traditional phone service, including lower costs, increased flexibility, and enhanced features. However, VoIP also has some potential security vulnerabilities that users need to be aware of.
In this guide, we will discuss some of the most common VoIP security vulnerabilities and how you can protect yourself from them. We will cover topics such as unsecured VoIP protocols, weak encryption methods, and social engineering attacks. By the end of this guide, you should have a better understanding of the risks associated with using VoIP technology and what you can do to mitigate them.
## vulnerabilities
Unsecured VoIP Protocols
One of the most common security vulnerabilities associated with VoIP is the use of unsecured protocols. Many VoIP providers use outdated or inadequately secured protocols to transmit voice data, which leaves users vulnerable to a number of different types of attacks. For example, an attacker could eavesdrop on a conversation by intercepting the signal being transmitted between two devices using an unsecured protocol. Alternatively, an attacker could tamper with the signal or inject malicious code into it in order to take control of the devices involved in the call.
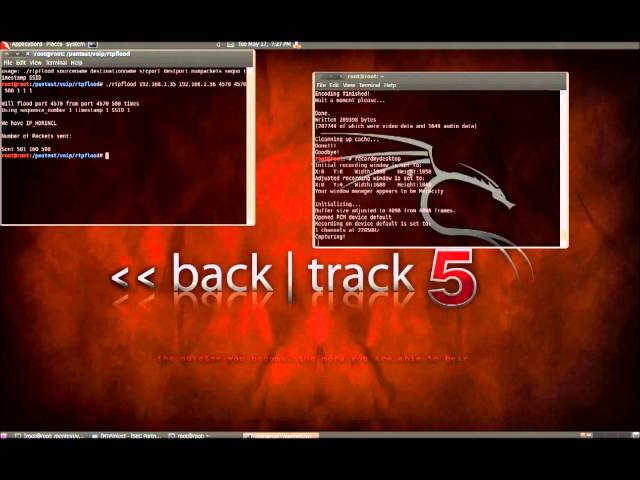
Some of the most commonly used unsecured protocols for VoIP include Session Initiation Protocol (SIP), Real-time Transport Protocol (RTP), and H.323. Many companies that offer VoIP services do not properly encrypt their traffic or authenticate their users, which makes it easy for attackers to exploit these insecure protocols.
To protect yourself from attacks that exploit unsecured VoIP protocols, you should only use companies that offerVoIP services that use industry-standard encryption methods such as Transport Layer Security (TLS) or Secure Real-time Transport Protocol (SRTP). You should also verify that your provider employs proper authentication measures such as two-factor authentication (2FA).
2FA is an authentication method that requires users to provide two pieces of evidence in order to prove their identity. This could include something you know like a password or PIN combined with something you have like a smart card or one-time code generated by an app on your smartphone
What is VoIP?
VoIP is an acronym for Voice over Internet Protocol—which means that instead of using a phone line from a phone company, VoIP uses the Internet to make and receive calls.
For the most part, making calls using VoIP is just like making any other phone call. You can dial a number and talk to somebody on the other end. The big difference is how the call is transmitted.
With traditional phone service (POTS), your voice is converted into an electrical signal and sent over copper wires to the person you’re calling. With VoIP, your voice is converted into digital signals and transmitted over the Internet.
The Vulnerabilities of VoIP
Voice over IP (VoIP) is a great way to save money on your phone bill, but it’s not without its risks. VoIP calls are transmitted over the public internet, which makes them susceptible to the same security risks as any other data that travels over the internet. In this article, we’ll take a look at some of the most common VoIP vulnerabilities and what you can do to protect yourself.
Spoofing
Spoofing is one of the most common types of attacks on VoIP systems. Spoofing is when a caller ID is faked to make it look like the call is coming from a trusted source when it’s not. The attacker can use spoofing to make it seem like they are calling from a legitimate business or from someone you know. This can be used to gain information from you or to get you to transfer money to them.
To protect against spoofing, you need to be aware of some common indicators that a call may be spoofed. If you get a call from an unfamiliar number, be suspicious. You can also try to call the number back to see if you get the same person on the other end. If the caller seems to have inside information about you or your business, they may be trying to gathered information through social engineering. Be suspicious of any unexpected calls, even if they appear to be from someone you know. If something seems off, hang up and call the person back using a known number.
Eavesdropping
Eavesdropping is one of the most common VoIP vulnerabilities. It’s also one of the easiest to exploit. All an attacker needs is a way to access your network and the right software. Once they’re in, they can start intercepting your calls and listening in on your conversations.
To defend against this type of attack, you need to make sure that your VoIP system is properly encrypted. Look for a system that uses AES or SSL/TLS encryption. This will make it much harder for an attacker to eavesdrop on your calls.
You should also consider using a VPN. A VPN encrypts all of the traffic on your network, including your VoIP calls. This makes it much harder for an attacker to snoop on your conversations.
Denial of Service
One of the most common types of attacks on VoIP networks is Denial of Service (DoS). A DoS attack attempts to render a service, such as VoIP, inaccessible to legitimate users. There are a number of ways to carry out a DoS attack, but the most common is to flood the target with so much traffic that it can’t keep up with the demand and shuts down.
DoS attacks on VoIP networks are usually carried out by botnets — large networks of infected computers that are controlled by attackers. The computers in a botnet are typically infected with malware that allows the attacker to take remote control of them. Once an attacker has control of a large number of computers, they can use them to carry out a DoS attack.
DOS attacks can be difficult to defend against because they don’t usually require any sophisticated skills or tools. All an attacker needs is a large network of infected computers and the ability to send commands to them. However, there are a few things you can do to protect yourself from these types of attacks:
– Use firewalls: Firewalls can help block unwanted traffic from reaching your network.
– Use intrusion detection and prevention systems: These systems can help identify and block attacks as they’re happening.
– Limit access to your network: Only allow trusted users and devices access to your network. This will help prevent botnets from gaining access in the first place.
How to Secure Your VoIP System
Voice over Internet Protocol, or VoIP, is a popular way to make calls over the internet. However, VoIP systems are often vulnerable to attack. In this article, we’ll discuss some of the most common VoIP vulnerabilities and how you can protect your VoIP system.
Use a VPN
businesses should consider using a VPN in conjunction with VoIP to secure their communications. A VPN, or Virtual Private Network, encrypts all data that travels between your business location and the VoIP provider, making it impossible for anyone to listen in or intercept your calls.
Use Encryption
In order to keep your VoIP calls secure, you need to use encryption. VoIP encryption scrambles your call data so that it can only be decoded by the person you’re speaking to. This prevents anyone who intercepts your call from being able to listen in.
There are several different types of VoIP encryption, each with its own benefits and drawbacks. The most common type of encryption is Transport Layer Security (TLS), which is used by many websites and apps to protect user data. TLS is very effective at encrypting VoIP calls, but it can slow down your connection and cause problems with call quality.
Another type of encryption is Secure Real-Time Transport Protocol (SRTP), which is specifically designed for VoIP calls. SRTP is less likely to cause problems with call quality, but it’s not as widely supported as TLS.
You should also make sure that your VoIP provider uses strong authentication methods, such as two-factor authentication (2FA). This will help to prevent anyone who doesn’t have the correct login credentials from being able to access your account.
Finally, you should consider using a Virtual Private Network (VPN) to encrypt all of the traffic on your device, not just your VoIP calls. A VPN will add an extra layer of security to your device and make it more difficult for attackers to snoop on your traffic.
Use a Firewall
A firewall is a VoIP security best practice that can protect your IP PBX from many different kinds of attacks, including denial of service (DoS) attacks, toll fraud, and viruses. A firewall can also help to protect your network from unauthorized access by restricting inbound and outbound traffic to specific IP addresses and ports.
There are a few different types of firewalls that can be used to protect a VoIP system, including:
-Network firewalls: These firewalls are designed to protect an entire network from various threats. Network firewalls can be hardware- or software-based, and they are typically deployed at the edge of a network.
-Host-based firewalls: Host-based firewalls are installed on individual computers or servers and are designed to protect those specific devices from being compromised.
-Application-level gateways: Also known as application-level proxies, these devices inspect traffic at the application layer of the OSI model to ensure that only legitimate traffic is allowed through.
Conclusion
As you can see, there are a number of VoIP vulnerabilities that you need to be aware of. By taking the time to understand these vulnerabilities, you can help to keep your VoIP system secure. If you are concerned about any of these vulnerabilities, be sure to contact a security professional who can help you to mitigate them.